There are always good reasons to install a stock factory ROM for a phone, I can think of some of them:
- clean factory reset before selling the device
- install the latest firmware
- install another official firmware (unbrand the phone)
- downgrade the firmware
- unbrick the device after a failed hack
Here’s what I’ve done.
Disclaimer
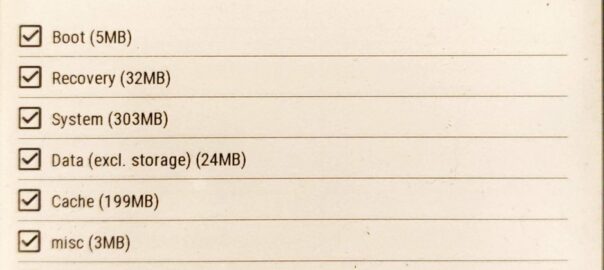
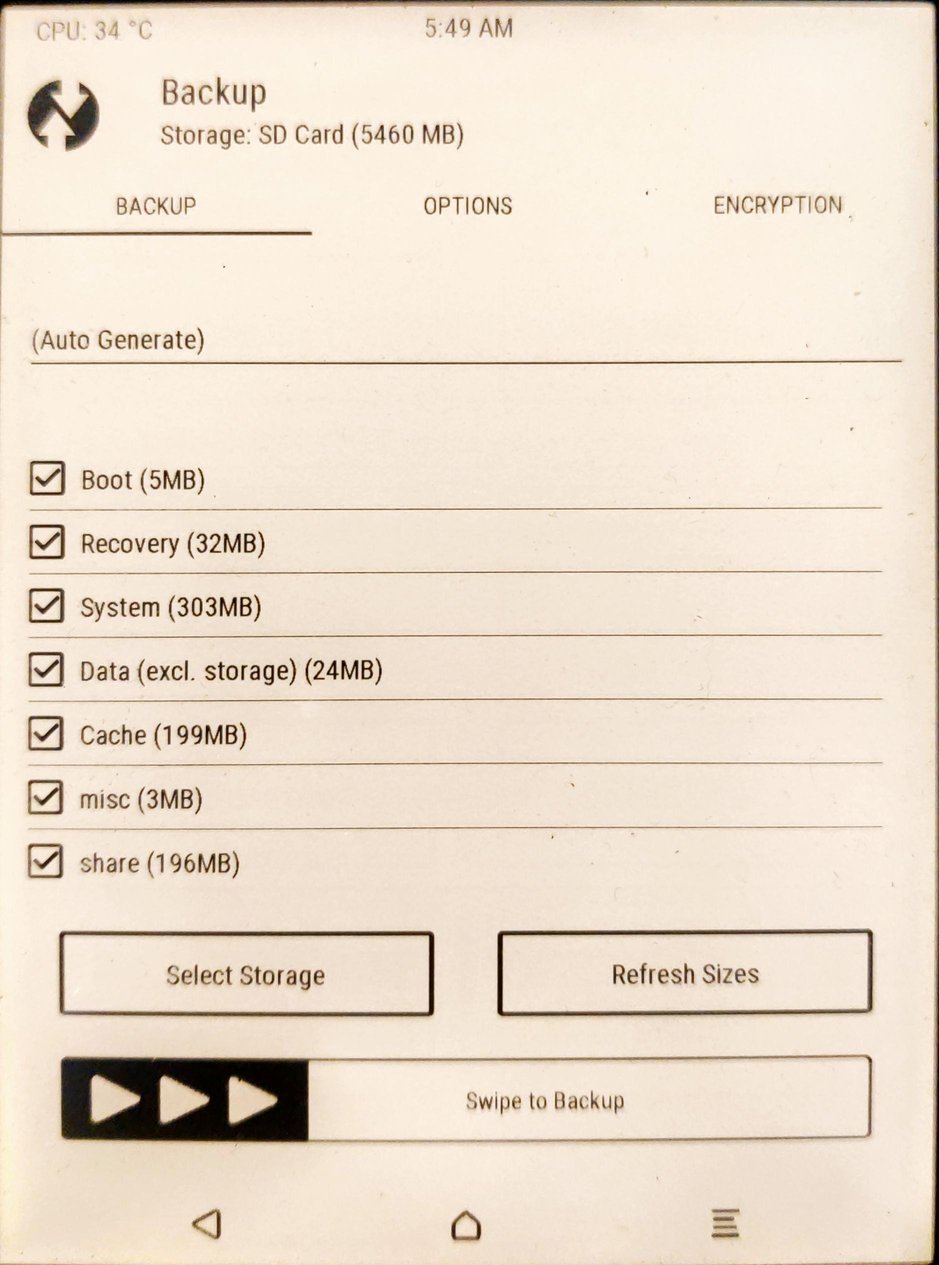
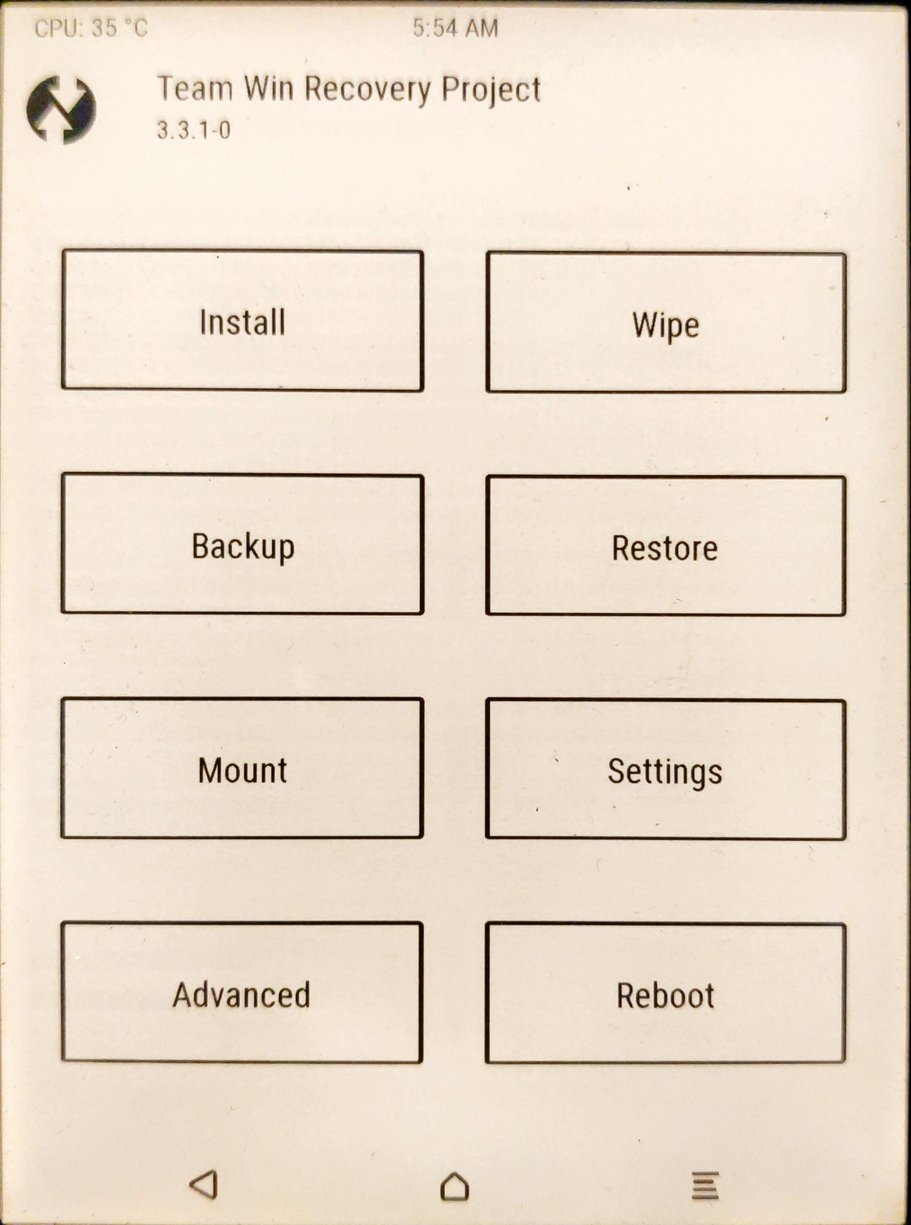
This is a complete reset, all the data will be lost, make a backup if you care about your data.
I am not responsible if you brick / ruin your device in any way. Basic computer skills required. Proceed with caution. I cannot be held responsible if anything goes wrong.
Device details
Model name: Galaxy A7 (2018)
Model code: SM-A750FN
Prerequisites
I’m working on Ubuntu 21.10, so I’ve to install these packages
$ apt install heimdall-flash lz4Download original firmware
You can find original firmwares from various sites, in my case, I downloaded A750FNXXU5CUH2_A750FNOXM5CUH2_ITV.zip from https://www.sammobile.com/samsung/galaxy-a7-2018/firmware/#SM-A750FN. I had to create an account, so maybe there are better options.
Extract all the files from the firmware file
Explanation: the downloaded zip contains some .md5 files. They are actually .tar files, so we have to untar them (for the sake of clarity I prefer to rename them before). Each .tar contains, for the most part, .lz4 files. We have to extract the content of those files, too.
$ mkdir tmp
$ cd tmp/
$ unzip ../A750FNXXU5CUH2_A750FNOXM5CUH2_ITV.zip
$ rename 's:.md5$::' *.md5
$ for f in *.tar; do tar xf "$f" && rm "$f"; done
$ for f in *.lz4; do lz4 -d "$f" && rm -f "$f"; done
Here’s the content my folder after the extraction:
$ ls -1R
.:
A7Y18LTE_EUR_OPEN.pit
boot.img
cache.img
cm.bin
hidden.img
meta-data
modem.bin
modem_debug.bin
odm.img
omr.img
param.bin
recovery.img
sboot.bin
system.img
userdata.img
vendor.img
./meta-data:
download-list.txt
fota.zip
Boot the phone in Odin mode / Download mode
- shutdown the device
- disconnect USB cable
- keep pressed Volume UP and Volume DOWN
- connect USB cable
Start the procedure of complete firmware replacement
Test heimdall detection of the device
$ heimdall detect
Device detected
Print and store the partition table
$ heimdall download-pit --output a7.pit
(the phone will reboot and you’ll have to enter in Odin mode again. The --no-reboot argument of heimdall works, but the subsequent command will fail even if launched with --resume, so let’s reboot anyway.)
The .pit file is a binary file, but we can inspect it with the right heimdall command
$ heimdall print-pit --file a7.pit >a7.pit-decoded
$ cat a7.pit-decoded
Check if the device partition table matches the firmware’s one
$ md5sum <(heimdall print-pit --file a7.pit) <(heimdall print-pit --file A7Y18LTE_EUR_OPEN.pit)
737ea1830f953bdd7eb5297cf095592d /dev/fd/63
737ea1830f953bdd7eb5297cf095592d /dev/fd/62
Associate each file to the right partition to flash, as stated in the .pit file
$ for f in *; do echo -n "# $f: "; { grep -B1 "$f" a7.pit-decoded || echo "__not found__"; } | head -1; done | column -s: -t
# a7.pit __not found__
# a7.pit-decoded __not found__
# A7Y18LTE_EUR_OPEN.pit __not found__
# boot.img Partition Name BOOT
# cache.img Partition Name CACHE
# cm.bin Partition Name CM
# hidden.img Partition Name HIDDEN
# meta-data __not found__
# modem.bin Partition Name RADIO
# modem_debug.bin Partition Name CP_DEBUG
# odm.img Partition Name ODM
# omr.img Partition Name OMR
# param.bin Partition Name PARAM
# recovery.img Partition Name RECOVERY
# sboot.bin Partition Name BOOTLOADER
# system.img Partition Name SYSTEM
# userdata.img Partition Name USERDATA
# vendor.img Partition Name VENDOR
The .pit files must not be flashed, the meta-data entry in the list is a directory, so everything has a match.
With these informations we can build our flash command
$ heimdall flash --pit A7Y18LTE_EUR_OPEN.pit --BOOT boot.img --CACHE cache.img --CM cm.bin --HIDDEN hidden.img --RADIO modem.bin --CP_DEBUG modem_debug.bin --ODM odm.img --OMR omr.img --PARAM param.bin --RECOVERY recovery.img --BOOTLOADER sboot.bin --SYSTEM system.img --USERDATA userdata.img --VENDOR vendor.img
In my case it took ~3 minutes. Then the phone will reboot. The first boot will take up to ~5 minutes so don’t worry and be patient.